


default search action
Welcome to dblp
Search dblp
Full-text search
- > Home
Please enter a search query
- case-insensitive prefix search: default
e.g., sig matches "SIGIR" as well as "signal" - exact word search: append dollar sign ($) to word
e.g., graph$ matches "graph", but not "graphics" - boolean and: separate words by space
e.g., codd model - boolean or: connect words by pipe symbol (|)
e.g., graph|network
Update May 7, 2017: Please note that we had to disable the phrase search operator (.) and the boolean not operator (-) due to technical problems. For the time being, phrase search queries will yield regular prefix search result, and search terms preceded by a minus will be interpreted as regular (positive) search terms.
Author search results
Likely matches
- Network Information Center
- First Birn
aka: Functional Imaging Research Schizophrenia Testbed-Biomedical Informatics Research Network - Federal Networking Council
- RHSCIR Network Imaging Group
- Dominantly Inherited Alzheimer Network (DIAN)
Venue search results
Likely matches
- International Conference on Computer Graphics and Interactive Techniques (SIGGRAPH)
- International Conference on Medical Image Computing and Computer-Assisted Intervention (MICCAI)
- Computer Networks
- International Conference for High Performance Computing, Networking, Storage and Analysis (SC)
- Journal of Network and Computer Applications
Refine list
refine by author
- no options
- temporarily not available
refine by venue
- no options
- temporarily not available
refine by type
- no options
- temporarily not available
refine by access 
- no options
- temporarily not available
refine by year
- no options
- temporarily not available
Publication search results
found 1,003,457 matches
- 2026
- Zhirun Zheng, Zhetao Li, Xuemin Shen:

Perturbation Based Privacy in Crowdsensing. Wireless Networks, Springer 2026, ISBN 978-3-031-95051-3, pp. 1-179 - Yuanjun Chai, Chao Ge, Yanpeng Shi, Zhinan Peng, Huiyan Zhang:

Impulse-based output consensus tracking of heterogeneous clustered networks subjected to unknown bounded cyber-attacks. Appl. Math. Comput. 509: 129660 (2026) - Hao Chen

 , Weicheng Cui
, Weicheng Cui :
:
Intergroup-based public goods games in complex networks with leader-driven other-regarding preferences. Appl. Math. Comput. 508: 129623 (2026) - Leonard Chidiebere Eze

 , Robert Jajcay, Jorik Jooken
, Robert Jajcay, Jorik Jooken :
:
On (k,g)-graphs without (g + 1)-cycles. Appl. Math. Comput. 508: 129645 (2026) - Qaisar Farhad, Mumtaz Hussain, Shou-Jun Xu:

Closeness spectra and structural uniqueness of special graph classes. Appl. Math. Comput. 509: 129666 (2026) - Yijie Huang, Yanhong Chen:

Investigating the evolutionary dynamics of cooperation on a dynamic network: the influence of aspiration-driven structural adaptations. Appl. Math. Comput. 509: 129670 (2026) - Zejun Huang, Xinwei Zhang:

The maximum number of maximum dissociation sets in potted graphs. Appl. Math. Comput. 508: 129618 (2026) - Xin Jin, Xiaojie Chen, Zhengxin Wang:

Quasi-synchronization of multiplex networks under deception attacks via event-triggered impulsive protocol. Appl. Math. Comput. 508: 129635 (2026) - Ajay Kumar, V. V. M. S. Chandramouli:

Study of reduced Chialvo map with electromagnetic flux: Dynamics and network behavior. Appl. Math. Comput. 509: 129650 (2026) - Tao Liu, Bolin Ding:

A radial basis function neural network approach for solving a diffusion partial differential equation efficiently. Appl. Math. Comput. 509: 129651 (2026) - Suoxia Miao, Housheng Su

 :
:
Consensus of different-order switched multi-agent systems on matrix-weighted networks. Appl. Math. Comput. 508: 129610 (2026) - Vijayakumar Muthusamy

 :
:
Augmented input-output finite time stabilization and tracking control for networked control systems via adaptive event-triggered mechanism. Appl. Math. Comput. 508: 129624 (2026) - Jiahui Song

 , Zaiwu Gong:
, Zaiwu Gong:
The power of gaps: Multilayer mechanisms and source tracing of complex dynamics in higher-order networks. Appl. Math. Comput. 508: 129625 (2026) - Qiuyue Tan, Haizhen Qiu, Yiqiao Wang, Kan Wang:

An identifying operation on a 1-planar graph with an application to acyclic coloring. Appl. Math. Comput. 508: 129614 (2026) - Qingfang Ye, Fengwei Li:

The minimum atom-bond sum-connectivity index of graphs with given degree sequence. Appl. Math. Comput. 509: 129667 (2026) - Shuo Zhang, Lu Liu, Chunhua Wang, Xiaomeng Zhang, Rong Ma:

Multistability and global attractivity for fractional-order spiking neural networks. Appl. Math. Comput. 508: 129617 (2026) - Qifan Zhang, Shuming Zhou:

Conditional (edge) neighbor connectivity of hierarchical star networks. Appl. Math. Comput. 509: 129644 (2026) - Ruy Fabila Monroy

 , Rosna Paul, Jenifer Viafara-Chanchi, Alexandra Weinberger:
, Rosna Paul, Jenifer Viafara-Chanchi, Alexandra Weinberger:
On the rectilinear crossing number of complete balanced multipartite graphs and balanced layered graphs. Comput. Geom. 130: 102199 (2026) - F. N. U. Shariful, Justin Weathers, Anirban Ghosh

 , Giri Narasimhan:
, Giri Narasimhan:
Engineering an algorithm for constructing low-stretch geometric graphs with near-greedy average degrees. Comput. Geom. 130: 102201 (2026) - P. Dhavakumar, Shanmugasundaram Vengadeswaran:

Software defect prediction using graph sample and aggregate-attention network optimized with nomadic people optimizer for enhancing the software reliability. Comput. Stand. Interfaces 95: 104033 (2026) - Francisco Lopez-Gomez

 , Rafael Marín López, Gabriel López Millán
, Rafael Marín López, Gabriel López Millán , Dan García-Carrillo
, Dan García-Carrillo , John Preuß Mattsson
, John Preuß Mattsson , Göran Selander:
, Göran Selander:
Towards a new standard for network access authentication: EAP-EDHOC. Comput. Stand. Interfaces 95: 104037 (2026) - Min Xie

 , Yong Yu, Ruonan Chen
, Yong Yu, Ruonan Chen , Yanqi Zhao, Jianting Ning
, Yanqi Zhao, Jianting Ning , Xiaoyi Yang, Zoe L. Jiang:
, Xiaoyi Yang, Zoe L. Jiang:
Multiuser data integrity auditing atop blockchain with secure user revocation for cognitive IoT networks. Comput. Stand. Interfaces 95: 104042 (2026) - Yuxin Wu, Guofeng Deng:

Aspect-level sentiment analysis based on graph convolutional networks and interactive aggregate attention. Comput. Speech Lang. 95: 101819 (2026) - Fan Yang, Tan Zhu, Jing Huang, Zhilin Huang, Guoqi Xie:

A novel graph kernel algorithm for improving the effect of text classification. Comput. Speech Lang. 95: 101818 (2026) - Emmanuel Arrighi, Niels Grüttemeier, Nils Morawietz, Frank Sommer

 , Petra Wolf:
, Petra Wolf:
Multi-parameter analysis of finding minors and induced subgraphs in edge-periodic temporal graphs. Discret. Appl. Math. 378: 102-119 (2026) - Francisca Andrea Macedo França, André Ebling Brondani

 , Daniel A. Jaume
, Daniel A. Jaume :
:
Graphs with exactly three main eigenvalues. Discret. Appl. Math. 378: 49-64 (2026) - J. J. García-Dávila, Jesús Leaños, J. M. Pacheco-Torres:

Distribution of the null coefficients of the differential polynomial of the tree graphs. Discret. Appl. Math. 378: 19-26 (2026) - Yanfang Liang, Baoyindureng Wu

 :
:
Cycle isolation in graphs. Discret. Appl. Math. 378: 1-11 (2026) - Yingzhi Tian

 , Jixiang Meng:
, Jixiang Meng:
A survey on the vertex-(edge-)k-maximal graphs and the k-vertex-(edge-)connected graphs with redundant subgraphs. Discret. Appl. Math. 378: 125-135 (2026) - Songnian Xu, Jinxing Zhao

 :
:
A characterization of graphs with two types of eigenvalue multiplicities equal to n-d-1. Discret. Appl. Math. 378: 37-48 (2026)
skipping 1,003,427 more matches
loading more results 
failed to load more results, please try again later
About dblp
The dblp computer science bibliography provides open bibliographic information on major computer science journals and proceedings. Originally created at the University of Trier in 1993, dblp is now operated and further developed by Schloss Dagstuhl. For more information check out our F.A.Q.
dblp statistics
- # of publications: 8,044,423
- # of authors: 3,868,132
- # of conferences: 6,934
- # of journals: 1,881
XML data
You may download the raw dblp data in a single XML file. A simple DTD is available. The paper DBLP - Some Lessons Learned documents technical details of this XML file. In the appendix DBLP XML Requests you may find the description of a primitive dblp query API. All metadata is released as open data under CC0 1.0 license. 
RSS feeds

manage site settings
To protect your privacy, all features that rely on external API calls from your browser are turned off by default. You need to opt-in for them to become active. All settings here will be stored as cookies with your web browser. For more information see our F.A.Q.
Unpaywalled article links
Add open access links from  to the list of external document links (if available).
to the list of external document links (if available).
Privacy notice: By enabling the option above, your browser will contact the API of unpaywall.org to load hyperlinks to open access articles. Although we do not have any reason to believe that your call will be tracked, we do not have any control over how the remote server uses your data. So please proceed with care and consider checking the Unpaywall privacy policy.
Archived links via Wayback Machine
For web page which are no longer available, try to retrieve content from the  of the Internet Archive (if available).
of the Internet Archive (if available).
Privacy notice: By enabling the option above, your browser will contact the API of archive.org to check for archived content of web pages that are no longer available. Although we do not have any reason to believe that your call will be tracked, we do not have any control over how the remote server uses your data. So please proceed with care and consider checking the Internet Archive privacy policy.
Reference lists
Add a list of references from  ,
,  , and
, and  to record detail pages.
to record detail pages.
load references from crossref.org and opencitations.net
Privacy notice: By enabling the option above, your browser will contact the APIs of crossref.org, opencitations.net, and semanticscholar.org to load article reference information. Although we do not have any reason to believe that your call will be tracked, we do not have any control over how the remote server uses your data. So please proceed with care and consider checking the Crossref privacy policy and the OpenCitations privacy policy, as well as the AI2 Privacy Policy covering Semantic Scholar.
Citation data
Add a list of citing articles from  and
and  to record detail pages.
to record detail pages.
load citations from opencitations.net
Privacy notice: By enabling the option above, your browser will contact the API of opencitations.net and semanticscholar.org to load citation information. Although we do not have any reason to believe that your call will be tracked, we do not have any control over how the remote server uses your data. So please proceed with care and consider checking the OpenCitations privacy policy as well as the AI2 Privacy Policy covering Semantic Scholar.
OpenAlex data
Load additional information about publications from  .
.
Privacy notice: By enabling the option above, your browser will contact the API of openalex.org to load additional information. Although we do not have any reason to believe that your call will be tracked, we do not have any control over how the remote server uses your data. So please proceed with care and consider checking the information given by OpenAlex.
retrieved on 2025-08-16 16:17 CEST from data curated by the dblp team
 all metadata released as open data under CC0 1.0 license
all metadata released as open data under CC0 1.0 license
see also: Terms of Use | Privacy Policy | Imprint


 Google
Google Google Scholar
Google Scholar Semantic Scholar
Semantic Scholar Internet Archive Scholar
Internet Archive Scholar CiteSeerX
CiteSeerX ORCID
ORCID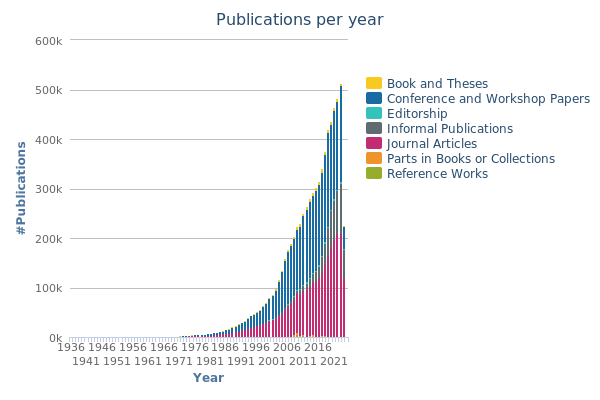
![[rss]](https://dblp1.uni-trier.de/img/rss.dark.16x16.png)








Social media links